The Art of Deception

Although many years have passed since then, I’m pretty sure it was 2003 when I read Kevin Mitnick’s book The Art of Deception. In it, he describes several real and hypothetical “hacking” cases, illustrating that humans are the weakest link in any secure system, thus a very good target for such attacks. The whole concept is called social engineering.
During that period, I was an undergraduate student. One afternoon, while we were hanging out at my apartment with some friends, we started talking about Mitnick’s book that I was reading these days, so I explained the concept of social engineering to them.
The conversation was interrupted by another friend of ours, who came into the apartment frustrated. He was coming from his travel agent -located just a few minutes from my home- where he went to get his plane ticket. When he arrived there, he discovered that the agent’s internet connection was down, therefore couldn’t retrieve the ticket information and print it, so he had to wait until that was fixed.
By the way, although DSL connections existed, the most common internet connections at that time in Greece were PSTN (remember their sound?) & ISDN. The travel agent had an ISDN connection. How we knew that?
They told my friend something along the lines of “we are waiting for the ISDN guy of company X to come back; he was here about an hour ago and said he had to go and check something at the exchange”.
I’m sure that a lot of you would have the exact same idea! :)
I quickly fired up my own ISDN connection, found the agent’s details and gave them a call.
Me: Hi, I’m calling from company X; you’re still having issues with your ISDN connection, right?
Agent: Yes, that’s correct.
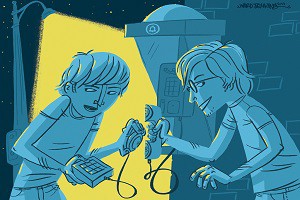
M: As I can see in my records, he had an engineer over at your place earlier today which informed us that there is a problem with Y (something that would be difficult to follow without a technical background).
(after a couple of minutes)
M: The problem should now be fixed; please, try to connect.
A: I still get the same error.
M: Then, we need to test with your credentials, since on our end everything seems fine. Can you please give me your username and password to try them out and also make sure you are using the correct combination?
A: Sure (…)
After thanking and telling him that I would run some tests and call him straight back, I tried his credentials using my ISDN modem. They worked. A few minutes later, I called him back and explained that I was actually a student doing some research on security, found a good excuse about how I knew he had a problem with his internet connection, told him that I was sorry for wasting a few minutes of his day and advised him not to give sensitive information over the phone, to change his username & password, etc.
Of course, I immediately threw away the credentials (I did the whole thing just to try out if that whole thing worked) and never used them again — I never even tried them again just to test if he actually changed them, but that taught all of us a very important lesson. To always keep in mind that no matter how secure a computing system is, there is always a human available to screw it up!
The book might be old, Mitnick hacking days might be older, but such attacks still exist. The latest example that comes to mind is an attack against eBay, where the attackers stole “a database containing encrypted passwords and other non-financial data” (still a lot of personal data though).
How the attack was performed? “Cyberattackers compromised a small number of employee log-in credentials, allowing unauthorized access to eBay’s corporate network”.
They never had to hack eBay itself; they just had to hack some of its employees!
This story was originally published as part of my newsletter’s editorial and was also published on medium.
Images by mustified, wikipedia, and Ward Jenkins
